Cyber Resilience in Australia’s Digital Ecosystem
Bharadwaj D Jagannath
Senior Architect – Technology
Cybersecurity
Executive Summary
Cyber resilience in Australia is no longer an abstract security ideal—it is an operational, regulatory and reputational requirement. The Australian Signals Directorate (ASD)’s Annual Cyber Threat Report 2024–25 describes a threat environment where credential theft, ransomware, and data breaches continue to rise, with the ASD’s Australian Cyber Security Centre (ACSC) responding to more than 1,200 incidents and receiving over 84,700 cybercrime reports (roughly one every six minutes). Meanwhile, the Office of the Australian Information Commissioner (OAIC) reporting confirms that notifiable data breaches remain at record levels, reinforcing that privacy impact is now a first-order business risk.
The 2025 breach set provides a particularly instructive signal: incidents range from misconfigured public exposure and third-party supplier failures to ransomware-driven exfiltration and compromise of sensitive justice-sector documents. Collectively, these events show that the most damaging breaches are rarely ‘zero-day miracles’; they are control-plane failures—identity, vendor trust boundaries, and detection/recovery maturity. This report translates those lessons into an Australian-specific resilience architecture and a pragmatic infrastructure blueprint ready for executive action.
2025 Breach Reality Check: What the Biggest Incidents Reveal
The most valuable part of breach reporting is not the headline impact—it is the repeatable pattern. 2025’s Australian incidents highlight four recurring systemic issues that most enterprises still under-engineer:
- Public exposure and weak content governance in digital channels (web portals, attachments, registry systems).
- Third-party data handling and supplier security gaps that bypass ‘internal controls’.
- Extortion economics: ransomware increasingly pairs encryption with exfiltration (double/triple extortion).
- High-sensitivity data domains (justice, health, education) where confidentiality failures cascade into physical safety and legal harm.
2025 Key Case Studies
Australian Human Rights Commission — April 2025
What happened: Attachments submitted via web forms were exposed and accessed for a period, potentially including highly sensitive personal and health-related information.
Key takeaway: Treat citizen-facing content workflows as critical systems: secure-by-default storage, strict access control, and continuous scanning for exposure/misconfiguration.
Resilience mapping: Assume Breach Readiness (continuous monitoring for exposure) + Identity as the Control Plane (least privilege for admin/content roles).
Nine Newspapers — March 2025
What happened: Subscriber personal data exposure attributed to a third-party provider; internal systems reportedly remained secure.
Key takeaway: Trust boundaries are contractual and technical: supplier risk must include technical enforcement (data minimization, segmentation, audit telemetry, and measurable SLAs).
Resilience mapping: Supply-Chain Vigilance (continuous assurance + integration controls) + Assume Breach Readiness (vendor incident cooperation).
NSW Department of Communities and Justice — April 2025
What happened: Thousands of sensitive court documents were reportedly downloaded from an online registry environment.
Key takeaway: For high-impact domains, ‘confidentiality is safety’: enforce strong identity controls, access review, anomaly detection for bulk download, and robust logging for forensics.
Resilience mapping: Identity as the Control Plane (strong auth + policy) + Assume Breach Readiness (telemetry and rapid containment).
Fullerton Hotels and Resorts (Sydney property) — April 2025
What happened: Ransomware group claimed theft of large volumes of corporate documents (contracts, IDs, financials) with extortion pressure.
Key takeaway: Engineer for extortion: isolate sensitive repositories, implement immutable backups, and implement DLP/egress controls to detect and throttle mass exfiltration.
Resilience mapping: Assume Breach Readiness (detect/contain/recover) + Supply-Chain Vigilance (contractual & data-handling controls).
University of Notre Dame Australia — February 2025
What happened: Ransomware group claimed exfiltration including personal data and potentially medical records.
Key takeaway: Reduce blast radius with segmentation and least privilege; ensure rapid identity containment, incident triage, and validated recovery for core services.
Resilience mapping: Identity as the Control Plane + Assume Breach Readiness.
Strategic Analysis: The Architecture of Resilience
The case studies reinforce that Australia’s breach mechanics converge on three engineering truths: identity is the control plane; supplier trust must be explicitly bounded; and compromise must be assumed. A resilient enterprise architecture therefore requires three mutually reinforcing pillars:

1) Identity as the Control Plane (Zero Trust in Practice)
Australian breach patterns increasingly begin with credential compromise, privileged misuse, or insufficient session governance. Zero Trust becomes real only when identity, device health and session risk are continuously evaluated and enforced.
- Adopt phishing‑resistant MFA (FIDO2/WebAuthn/passkeys) for privileged access and remote entry points; retire SMS/voice and reduce push‑fatigue exposure.
- Implement tiered administration and PAM: isolate admin workstations, enforce just‑in‑time elevation, and gate privileged actions with step‑up authentication and session recording.
- Harden token/session security: shorten token lifetimes where feasible, monitor anomalous OAuth grants, and restrict legacy authentication.
- Engineer for bulk-access risk: enforce download throttles, conditional access, and anomaly detection on high-sensitivity repositories (e.g., registries, portals, case management).
2) Supply-Chain Vigilance (Trust Boundaries are Contractual and Technical)
Supplier incidents demonstrate that internal security can be bypassed when external processors, marketing platforms, or managed services hold or access customer data. Contracts are necessary but insufficient without technical enforcement.
- Treat integrations as untrusted: isolate connectivity, enforce least privilege at API/tenant boundaries, and segment managed access paths.
- Move from questionnaires to continuous assurance: validate control evidence and monitor exposed credentials, cloud misconfigurations and external attack surface.
- Mandate secure-by-design: software bills of materials (SBOMs), vulnerability disclosure, and patch/notification SLAs for products and suppliers.
- Contract for incident cooperation: clear reporting timelines, forensic support, and audit log access to meet SOCI/NDB/APRA expectations where applicable.
3) Assume Breach Readiness (Detect, Contain, Recover)
Ransomware-driven exfiltration and public exposure events require ‘assured recovery’ and ‘assured detection’. The goal is to reduce dwell time, constrain blast radius, and restore critical services within tolerances.
- Unified telemetry: ingest endpoint detection and response (EDR) logs, identity, network, and cloud audit data into a security information and event management (SIEM) platform; prioritize identity misuse and data-access anomalies.
- Containment engineering: segmentation, lateral movement restriction (SMB/WinRM/RDP), hardened admin planes and application control where feasible.
- Exfiltration controls: apply DLP/egress monitoring, high-risk download alerts, and encryption/key management for sensitive datasets.
- Immutable recovery: implement ‘3‑2‑1‑1‑0’ backups with offline/immutable copies, separate admin domains, and routine restore validation.
Blueprint for a Cyber‑Resilient IT Infrastructure
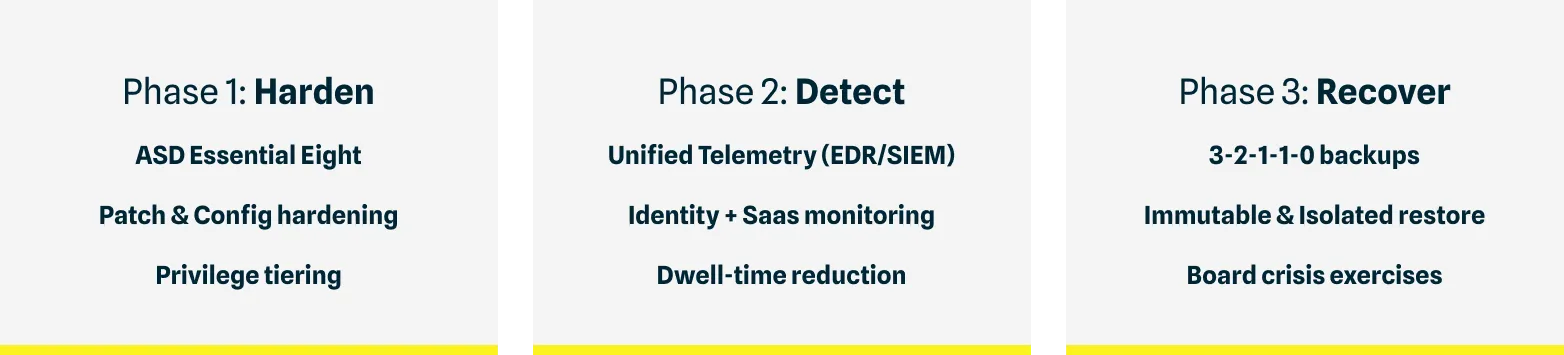
Elevating cybersecurity from a technical concern to a measurable business advantage demands deliberate investment. Australian executives and CIOs should adopt a three‑phase program aligned to ASD guidance and current regulatory expectations.
Australian Regulatory Anchors: Privacy Act (NBD) | SOCI Act Incident Reporting | APRA CPS 234/230 | ASD ISM / Essential Eight | Cyber Security Strategy 2023 - 2030
Phase 1: Harden the Foundation (Essential Eight with maturity)
- Set Essential Eight maturity targets per asset class and track drift via configuration compliance.
- Reduce identity attack paths: phishing-resistant MFA for admins, least privilege, remove shared accounts and legacy protocols.
- Patch with service level objectives (SLOs): automate and measure time-to-remediate for critical CVEs; prioritize internet-facing and edge devices.
Phase 2: Visibility and Detection (Closing the Detection Gap)
- Instrument the control plane: centralise identity, cloud and SaaS logs; ensure audit coverage for admin actions, data export and OAuth grants.
- Detect ‘living off the land’: analytics for abnormal admin tool use, privilege escalation and high‑volume data access.
- Operationalize response: SOCI/NDB decision trees, containment playbooks (identity lock-down, tenant isolation, key rotation), and rehearsals.
Phase 3: Resilience and Recovery (Prove restoration of critical operations)
- Treat identity and data platforms as critical operations: set recovery objectives and disruption tolerances; validate via scenario testing.
- Implement immutable backups and recovery enclaves: isolate backup administration, pre-stage clean-room restore, validate restoration quarterly.
- Board-level wargaming: executive decision points on extortion, reporting and communications; convert lessons into risk treatments.
Conclusion
The 2025 breach set reinforces a practical truth: cyber resilience is an engineering discipline with governance consequences. Australian organizations that design identity as the control plane, enforce supplier trust boundaries, and institutionalize detect/contain/recover will reduce the likelihood that a breach becomes a crisis—and will be better positioned to meet regulator, customer, and board expectations. Synechron partners with Australian financial services and enterprise organizations to translate these priorities into funded, executable programs—from architecture design and Essential Eight uplift to managed detection and board-level resilience reporting.
References
- Otto IT: ‘Biggest Australian Cyber Breaches in 2025’ (16 June 2025) (https://www.ottoit.com.au/blog/biggest-australian-cyber-breaches-in-2025/)
- ASD Annual Cyber Threat Report 2024–25 (cyber.gov.au)
- OAIC Notifiable Data Breaches Report (July–December 2024) (oaic.gov.au)
- SOCI Act mandatory incident reporting guidance (cyber.gov.au)
- APRA CPS 230 Operational Risk Management (apra.gov.au)
